>Web_Hacking_
- OWASP TOP 10 -

Web application Hacking is the art of finding, and exploiting vulnerabilties within
a web appliction. Whether it is finding vulnerabilties that are server side, or client side.
 There are many different types of vulnerabilties that we have to look out for when testing a
web appliction. OWASP (the OPEN Web Application Security Project) creates standards (updated
regularly)
that they recommend everyone to know and keep on top of. These are Known as the OWASP TOP
10
There are many different types of vulnerabilties that we have to look out for when testing a
web appliction. OWASP (the OPEN Web Application Security Project) creates standards (updated
regularly)
that they recommend everyone to know and keep on top of. These are Known as the OWASP TOP
10

| Attack | Type |
|---|---|
| A1 | Injection |
| A2 | Broken Authentication |
| A3 | Sensetive Data Exposure |
| A4 | XML External Entities (XXE) |
| A5 | Broken Authentication Control |
| A6 | Security Misconfiguration |
| A7 | Cross-Site Scripting |
| A8 | Insecure Deserialization |
| A9 | Using Components with known Vulnerabilites |
| A10 | Insuffiecient logging & Monitoring |
A1 Injection

Injection flaws, such as SQL injection, LDAP injection, and CRLF injection, Command injection occur when an attacker sends untrusted data to an interpreter that is executed as a command without proper authorization.
-Mitigation-
Application security testing can easily detect injection flaws. Developers should use parameterized queries when coding to prevent injection flaws.
A2 Broken Authentication

Incorrectly configured user and session authentication could allow attackers to compromise passwords, keys, or session tokens, or take control of users’ accounts to assume their identities.
-Mitigation-
Multi-factor authentication, such as FIDO or dedicated apps, reduces the risk of compromised accounts.
A3 Sensitive Data Exposure

Applications and APIs that don’t properly protect sensitive data such as financial data, usernames and passwords, or health information, could enable attackers to access such information to commit fraud or steal identities.
-Mitigation-
Encryption of data at rest and in transit can help you comply with data protection regulations.
A4 XXE (XML External Entities)

Poorly configured XML processors evaluate external entity references within XML documents. Attackers can use external entities for attacks including remote code execution, and to disclose internal files and SMB file shares.
-Mitigation-
Static application security testing (SAST) can discover this issue by inspecting dependencies and configuration.
A5 Broken Access Contorl

Improperly configured or missing restrictions on authenticated users allow them to access unauthorized functionality or data, such as accessing other users’ accounts, viewing sensitive documents, and modifying data and access rights.
-Mitigation-
Penetration testing is essential for detecting non-functional access controls; other testing methods only detect where access controls are missing.
A6 Security Misconfiguration

This risk refers to improper implementation of controls intended to keep application data safe, such as misconfiguration of security headers, error messages containing sensitive information (information leakage), and not patching or upgrading systems, frameworks, and components.
-Mitigation-
Dynamic application security testing (DAST) can detect misconfigurations, such as leaky APIs, Default Creds.
A7 Cross-Site Scripting

Cross-site scripting (XSS) flaws give attackers the capability to inject client-side scripts into the application, for example, to redirect users to malicious websites.
-Mitigation-
Developer training complements security testing to help programmers prevent cross-site scripting with best coding best practices, such as encoding data and input validation.
A8 Insecure Deserialization

Insecure deserialization flaws can enable an attacker to execute code in the application remotely, tamper or delete serialized (written to disk) objects, conduct injection attacks, and elevate privileges.
-Mitigation-
Application security tools can detect deserialization flaws but penetration testing is frequently needed to validate the problem.
A9 Using Components With Known Vulnerabilites
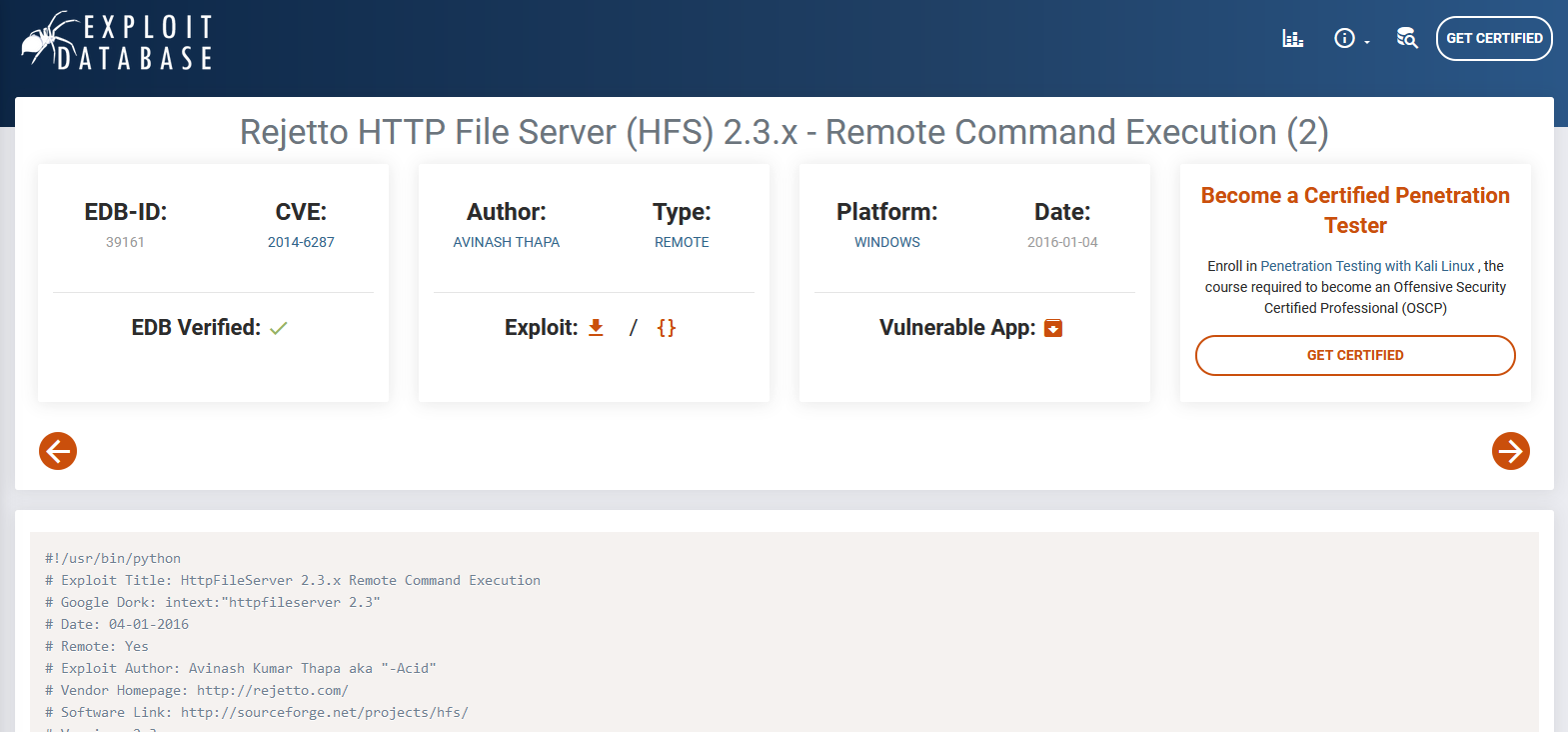
Developers frequently don’t know which open source and third-party components are in their applications, making it difficult to update components when new vulnerabilities are discovered. Attackers can exploit an insecure component to take over the server or steal sensitive data.
-Mitigation-
Software composition analysis conducted at the same time as static analysis can identify insecure versions of components.
A10 Insufficient Logging and Monitoring

The time to detect a breach is frequently measured in weeks or months. Insufficient logging and ineffective integration with security incident response systems allow attackers to pivot to other systems and maintain persistent threats.
-Mitigation-
Think like an attacker and use pen testing to find out if you have sufficient monitoring; examine your logs after pen testing.
